In the previous post, I had discussed about viewing installed or not installed devices. This post tells you how to install device driver for computer hardware devices.
PROCEDURE:
If you have installed WINDOWS operating system freshly, some on-board motherboard hardware devices such as display, audio, enternet, etc or if you have installed any additional hardware devices other than on-board hardware devices such as display, audio, enternet, etc need to be detected using drivers manually. All motherboard manufacturers provide drivers CD/DVD along with the motherboard when purchased.
If the drivers CD provided is AUTOPLAY (when CD/DVD is inserted into the CD/DVD drive the drivers application software runs automatically showing the list of motherboard drivers to be installed) select the devices from the list whose drivers needs to be installed and click on install or follow the instructions provided in the drivers application software till you finish the installation. Once finished installation restart the computer if needed to make the drivers detect the hardware devices.
If the CD/DVD provided is not AUTOPLAY, then follow the procedure as shown below.
Go to "START" and click on "SETTINGS" and click on "CONTROL PANEL" to open CONTROL PANEL window. Inside CONTROL PANEL window double click on "SYSTEM" to open "SYSTEM PROPERTIES" window. In the "SYSTEM PROPERTIES" window click on "HARDWARE" tab. Now you should be able to see a "DEVICE MANAGER" or hold the "WINDOWS KEY" and press "R" to open RUN window or go to "START" and click on "RUN" to open RUN window. Now type "devmgmt.msc" in the RUN window and click OK button or press "ENTER" key to open DEVICE MANAGER window.
In the DEVICE MANGER list look for "OTHER DEVICES". The drivers for the hardware devices list shown under "OTHER DEVICES" are not installed.
Now insert the drivers CD/DVD provided by the motherboard manufacturer into the CD/DVD drive. Now double click on the first device under the "OTHER DEVICES" list. A new window opens up showing the properties of that particular device. Now click on "RE-INSTALL DRIVER" button to open "HARDWARE UPDATE WIZARD" window.
Now select "No. not this time" and click "NEXT" to go to next step.
In the next step select "INSTALL FROM A LIST OR SPECIFIC LOCATION (ADVANCED)" and click on "NEXT" to go to next step.
Here select only "SEARCH REMOVABLE MEDIA (FLOPPY, CD_ROM...)" and click "NEXT" to begin installation of driver from the CD/DVD.
It automatically detects the drivers for the particular hardware device. Finally click "FINISH" to complete the device driver installation. Follow the same procedure for installing device driver for all the devices that are not installed and that are shown in the list under "OTHER DEVICES" list.
NOTE:
WINDOWS XP operating system service pack2 or WINDOWS XP operating system service pack3 comes with most motherboard hardware components drivers integrated. It all depends on the type and the manufacturer of the motherboard. As a result, some motherboards drivers need not be installed manually as the device drivers would have been installed when installing operating system. If some motherboard hardware drivers not installed during installation of WINDOWS operating system, then you need to install drivers manually for those hardware components.
Google documents, now with web fonts!
(Cross-posted from the Google Docs Blog)
In the past month we’ve made updates both big and small to Google Docs, and today we’re announcing one more: web fonts in Google documents. Often the best way to get your point across is to present your idea in a creative, captivating way. Today, we added over 450 new fonts to Google documents to make it easier for you to add a little something extra to whatever you create.
To use these new fonts, click on the font menu and select “Add fonts” at the very bottom, which will take you to a menu of all the Google Web Fonts available.
Once you’ve selected new fonts, you’ll be able to select them from the font menu.
Whether you’re looking for the perfect font for your first comic book or fancy handwriting for your wedding invitations, we hope you try out the new fonts and create some eye-catching documents.
In addition to hundreds of new fonts, we have a lot of other exciting updates to report:
In the past month we’ve made updates both big and small to Google Docs, and today we’re announcing one more: web fonts in Google documents. Often the best way to get your point across is to present your idea in a creative, captivating way. Today, we added over 450 new fonts to Google documents to make it easier for you to add a little something extra to whatever you create.
To use these new fonts, click on the font menu and select “Add fonts” at the very bottom, which will take you to a menu of all the Google Web Fonts available.
Once you’ve selected new fonts, you’ll be able to select them from the font menu.
Whether you’re looking for the perfect font for your first comic book or fancy handwriting for your wedding invitations, we hope you try out the new fonts and create some eye-catching documents.
In addition to hundreds of new fonts, we have a lot of other exciting updates to report:
- Google Drive launched as a place where you can create, share, collaborate, and keep all your stuff.
- There are now a few more options for inserting images in Docs, including inserting from Google Drive, searching for images from the LIFE Photo archive, or taking a snapshot with your webcam.
- Charts in spreadsheets now has support for minor gridlines and options to customize the formats of axis labels
- Accessibility in Docs got better with support for screenreaders in presentations and with the addition of NVDA to our list of supported screenreaders.
- From File > Page setup... you can now set the default page size for your new documents.
- It's now easier for speakers of right-to-left languages by automatically showing bidirectional controls when you type in a language that might use them.
- Apps Script had many improvements, including
- A new ScriptService for programmatically publishing your scripts and controlling when they run.
- A new function to find the root folder of someone’s Drive.
- An increase in the allowed attachment size in emails from 5MB to 25MB.
- An increase in the size of docs files you can create from 2MB to 50MB.
- There are now over 60 new templates in our template gallery.
How to know devices that are not properly installed in WINDOWS
In a computer any devices (example: DVD Writer, Display, Network card or Ethernet card or any external devices attached, etc) to work properly you need to install driver for that particular device. If you are facing problem with any devices not working properly or not getting detected properly, then you might have not installed the device driver properly or if already installed then the device driver might have been corrupted or the device hardware itself should be having a problem. All the computer hardware components or devices installed successfully or unsuccessfully can be viewed in DEVICE MANAGER.
To open DEVICE MANAGER, go to "START" and click on "SETTINGS" and click on "CONTROL PANEL" to open CONTROL PANEL window. Inside CONTROL PANEL window double click on "SYSTEM" to open "SYSTEM PROPERTIES" window. In the "SYSTEM PROPERTIES" window click on "HARDWARE" tab. Now you should be able to see a "DEVICE MANAGER" button.
Click on "DEVICE MANAGER" to open "DEVICE MANAGER" window to see the list of all installed devices in your computer.
The easiest way to open DEVICE MANAGER using keyboard is hold the "WINDOWS KEY" and press "R" to open RUN window or go to "START" and click on "RUN" to open RUN window. Now type "devmgmt.msc" in the RUN window and click OK button or press "ENTER" key to open DEVICE MANAGER window.
In the device list if any device which has a yellow question mark with exclamatory symbol on the left side of the device name as shown below, means that particular device is not installed. In order to make that particular device work properly, you should install driver for that device. In the below image you can see that there is a yellow question mark with exclamatory symbol next to "EHTERNET CONTROLLER". This means the network or ethernet driver is not installed. In order to make the ETHERNET CONTROL work, you need to install the ethernet or network driver.
Sometimes some devices will not work even if the driver is installed properly. For example, consider sound driver is installed properly and you are not be able to hear the sound. Then first check whether the volume control in the STATUS bar is MUTE. If it is not mute then re-installing the device driver for sound card. If you still cannot hear the sound, then chances are more that your sound card hardware device is not functioning properly.
To open DEVICE MANAGER, go to "START" and click on "SETTINGS" and click on "CONTROL PANEL" to open CONTROL PANEL window. Inside CONTROL PANEL window double click on "SYSTEM" to open "SYSTEM PROPERTIES" window. In the "SYSTEM PROPERTIES" window click on "HARDWARE" tab. Now you should be able to see a "DEVICE MANAGER" button.
Click on "DEVICE MANAGER" to open "DEVICE MANAGER" window to see the list of all installed devices in your computer.
The easiest way to open DEVICE MANAGER using keyboard is hold the "WINDOWS KEY" and press "R" to open RUN window or go to "START" and click on "RUN" to open RUN window. Now type "devmgmt.msc" in the RUN window and click OK button or press "ENTER" key to open DEVICE MANAGER window.
In the device list if any device which has a yellow question mark with exclamatory symbol on the left side of the device name as shown below, means that particular device is not installed. In order to make that particular device work properly, you should install driver for that device. In the below image you can see that there is a yellow question mark with exclamatory symbol next to "EHTERNET CONTROLLER". This means the network or ethernet driver is not installed. In order to make the ETHERNET CONTROL work, you need to install the ethernet or network driver.
Sometimes some devices will not work even if the driver is installed properly. For example, consider sound driver is installed properly and you are not be able to hear the sound. Then first check whether the volume control in the STATUS bar is MUTE. If it is not mute then re-installing the device driver for sound card. If you still cannot hear the sound, then chances are more that your sound card hardware device is not functioning properly.
Transfer data or content from one IDE hard disk to another IDE hard disk (Part 2)
PROCEDURE FOR CONNECTING TWO HARD DISK DRIVES TO TWO INDIVIDUAL IDE DATA CABLES
Usually the old motherboard has two IDE slots. You can connect one IDE slot to hard disk drive and the other IDE slot to IDE CD-ROM or Combo Drive OR DVD Drive
Now connect one end of the first IDE data cable to hard disk drive ( MASTER or first hard disk drive ) and the other end to first IDE port of the motherboard. Similarly connect second IDE data cable to the hard disk drive ( SLAVE or second hard disk drive )and the other end to the second free IDE slot on the motherboard as shown below.
Note :
(1) Jumper pin settings vary depending on the brand of the hard disk manufacturer.
(2) Most of the recent motherboards will have only one or will not have IDE slot. Instead will have only SATA port.
Transfer data or content from one IDE hard disk to another IDE hard disk (Part 1)
If you want to transfer large data or content from one hard disk to another hard disk, it just simply cannot be done by connecting two hard disk and switching on the system. Here is the procedure to copy data from hard disk to hard disk without any hassle.
Always remember whenever you want to copy from hard disk to hard disk, one hard disk must be MASTER and another hard disk must be SLAVE provided if you are connecting both hard disk to a single IDE data cable. If you are connecting two hard disk using two IDE data cables, then no need to make either of the hard disk as MASTER or SLAVE.
PROCEDURE IF YOU ARE CONNECTING TWO HARD DISK DRIVES USING SINGLE IDE DATA CABLE
In SEAGATE brand hard disk there is a jumper pin setting space between the IDE data cable slot where you fix the data cable to hard disk and power slot where you fix the power cable which comes from SMPS (power supply) as shown in the image below
Always remember whenever you want to copy from hard disk to hard disk, one hard disk must be MASTER and another hard disk must be SLAVE provided if you are connecting both hard disk to a single IDE data cable. If you are connecting two hard disk using two IDE data cables, then no need to make either of the hard disk as MASTER or SLAVE.
PROCEDURE IF YOU ARE CONNECTING TWO HARD DISK DRIVES USING SINGLE IDE DATA CABLE
In SEAGATE brand hard disk there is a jumper pin setting space between the IDE data cable slot where you fix the data cable to hard disk and power slot where you fix the power cable which comes from SMPS (power supply) as shown in the image below
Click here to see the purpose of using a jumper.
By default when you purchase a new hard disk the jumper pin is set to MASTER. To make the hard disk SLAVE remove the jumper pin (In Seagate Hard Disk Drive). Removing the jumper pin makes the hard disk to act as SLAVE.
All the hard disk manufacturers have a jumper pin settings diagram pasted on the hard disk as shown below.
All the hard disk manufacturers have a jumper pin settings diagram pasted on the hard disk as shown below.
After making sure that one hard disk is master and the other is slave, connect both hard disks as shown below.
Now you should be able to see the drives of both hard disk drives when you switch on the system.
The IDE data cable comes with two and three slots. You need to use three slots IDE cable if you are connecting two hard disk using only one IDE data cable. Out of three slots first slot should be connected to MOTHERBOARD also called as MAIN BOARD and the second free slot should be connected to MASTER hard disk drive and the third free slot has to be connect to SLAVE hard disk drive.
The IDE data cable comes with two and three slots. You need to use three slots IDE cable if you are connecting two hard disk using only one IDE data cable. Out of three slots first slot should be connected to MOTHERBOARD also called as MAIN BOARD and the second free slot should be connected to MASTER hard disk drive and the third free slot has to be connect to SLAVE hard disk drive.
There are chances when two hard disk are connected to a single IDE data cable, sometimes the SLAVE or MASTER hard disk will not be detected. In that case you have to connect both hard disk with individual IDE data cables ie, one ide data cable for MASTER hard disk drive and another IDE data cable for SLAVE hard disk drive.
Note:
(1) Jumper pin settings vary depending on the brand of the hard disk manufacturer.
(2) This method is not required if both hard disk drives are of SATA type. For SATA type hard disk drive, simply connect both hard disk drives to the mother board using individual SATA data cables. After connecting properly you should be able to see both hard disk drives when your windows boots up.
ttfautohint reaches its $30,000 funding target!
The Google Web Fonts team would like to congratulate Werner Lemberg on reaching his $30,000 funding target for ttfautohint.
Here is a fun video that explains what the project is about:
As a true open source project, it has sought contributions from across the industry. Google Web Fonts, FontLab and many individuals have given the project financial support. This week the Extensis WebINK team announced they have enabled Werner to reach his goal:
blog.webink.com/webink/extensis-webink-funds-open-source-ttfautohint-better-fonts-on-screen
You can download a graphical user interface for GNU/Linux and Windows today, a command line tool for Mac OS X, and of course the source code, from the project homepage:
www.freetype.org/ttfautohint
Posted by Dave Crossland, Font Consultant, Google Web Fonts Team
Here is a fun video that explains what the project is about:
As a true open source project, it has sought contributions from across the industry. Google Web Fonts, FontLab and many individuals have given the project financial support. This week the Extensis WebINK team announced they have enabled Werner to reach his goal:
blog.webink.com/webink/extensis-webink-funds-open-source-ttfautohint-better-fonts-on-screen
You can download a graphical user interface for GNU/Linux and Windows today, a command line tool for Mac OS X, and of course the source code, from the project homepage:
www.freetype.org/ttfautohint
Posted by Dave Crossland, Font Consultant, Google Web Fonts Team
Congratulations to All Designers of Tipos Latinos 2012!
¡Felicitaciones a todos los diseñadores de Tipos Latinos 2012!
The Google Web Fonts team would like to extend our congratulations to all designers selected for the Tipos Latinos 2012 Biennial.
El equipo de Google Web Fonts felicita a todos los diseñadores seleccionados en la Bienal Tipos Latinos 2012.
We were looking forward to seeing the results of this prestigious review of work by typeface designers across Latin America because we have been working with many of them.
Tenemos muchas ganas de ver los resultados de este prestigioso evento de diseño tipográfico de Latinoamérica, porque nosotros estuvimos trabajando con muchos de ellos.
Around a quarter of the typefaces featured are available in Google Web Fonts today – or very soon:
Aproximadamente un cuarto de las tipografías seleccionadas ya están disponibles en Google Web Fonts o lo estarán muy pronto:
The Alegreya family (including its Small Caps sister family) received a "Mención de Excelencia" (Recognition of Excellence) – congratulations Juan Pablo!
La familia Alegreya (que incluye una familia Small Caps) recibió la única "Mención de Excelencia" que en esta edición entregó el Jurado. ¡Felicitaciones, Juan Pablo!
You can read more about Tipos Latinos at tiposlatinos.com.
Pueden ver más sobre Tipos Latinos en tiposlatinos.com.
Posted by Dave Crossland, Font Consultant, Google Web Fonts
Publicado por Dave Crossland, Consultor tipográfico, Google Web Fonts
The Google Web Fonts team would like to extend our congratulations to all designers selected for the Tipos Latinos 2012 Biennial.
El equipo de Google Web Fonts felicita a todos los diseñadores seleccionados en la Bienal Tipos Latinos 2012.
We were looking forward to seeing the results of this prestigious review of work by typeface designers across Latin America because we have been working with many of them.
Tenemos muchas ganas de ver los resultados de este prestigioso evento de diseño tipográfico de Latinoamérica, porque nosotros estuvimos trabajando con muchos de ellos.
Around a quarter of the typefaces featured are available in Google Web Fonts today – or very soon:
Aproximadamente un cuarto de las tipografías seleccionadas ya están disponibles en Google Web Fonts o lo estarán muy pronto:
- Buenard, by Gustavo J. Ibarra (Argentina)
- Petrona, by Ringo Romei (Argentina)
- Ruluko, by A. Sanfelippo, A. Díaz y M. Hernández (Argentina, Colombia, Colombia)
- Unna, by Jorge de Buen (Mexico)
- Acme, by Juan Pablo del Peral (Argentina)
- Macondo, by John Vargas Beltrán (Colombia)
- Rufina, by Martín Sommaruga (Uruguay)
- Abril, by José Scaglione y Veronika Burian (Argentina)
- Alegreya, by Juan Pablo del Peral (Argentina)
- Almendra, by Ana Sanfelippo (Argentina)
- Andada, by Carolina Giovagnoli (Argentina)
- Bitter, by Sol Matas (Argentina)
- Delius, by Natalia Raices (Argentina)
- Rosarivo, by Pablo Ugerman (Argentina)
The Alegreya family (including its Small Caps sister family) received a "Mención de Excelencia" (Recognition of Excellence) – congratulations Juan Pablo!
La familia Alegreya (que incluye una familia Small Caps) recibió la única "Mención de Excelencia" que en esta edición entregó el Jurado. ¡Felicitaciones, Juan Pablo!
You can read more about Tipos Latinos at tiposlatinos.com.
Pueden ver más sobre Tipos Latinos en tiposlatinos.com.
Posted by Dave Crossland, Font Consultant, Google Web Fonts
Publicado por Dave Crossland, Consultor tipográfico, Google Web Fonts
How do you know if you can trust a website?
We use anti virus software, firewalls and spyware blocking software to keep our computers safe but it may not be enough. The truth is, if you continue to go to "bad websites" eventually something is going to get through and you'll be calling a company like ours for virus removal. So how can you avoid sites that may be "untrustworthy?"
Web of Trust is a free browser plugin that you should really look into. This great little utility ranks websites in a number of ways including trustworthiness, privacy, vendor reliability and child safety. It uses a simple, easy to recognize "traffic light" method of green, yellow and red color to inform you of the site's rating in any particular category. Based on the rating, you determine if you want to visit the site or not. It's simple, easy to use and gives you one more line of defense in the battle to keep your computer safe!
Is Web of Trust Perfect?
Of course it isn't perfect and it can't prevent you from going to bad sites if you choose to ignore the warning. We installed this on a customer's computer that was recently infected and cleaned up. After getting their computer back the customer called to explain that Web of Trust was giving a red light on a particular page that they liked to visit. It was a trustworthiness and privacy warning but the customer insisted that they wanted to visit that page. A few days later the computer was back in for a virus!
Web of Trust is not a replacement for an anti virus software, it's simply one more layer of security. If you've been using an anti virus software and find yourself getting infected perhaps you might want to consider a smarter anti virus solution, one that is actually monitored by professionals to make sure it's working! We also highly suggest that our customers consider backing up their data on a regular basis. A great solution is a cloud based backup that simply operates in the background so you don't have to worry about it. This way, if you do get a virus you can be sure that your music, movies, pictures and documents are safe and sound.
Blueline Network Solutions is a computer sales, service and repair facility providing service to consumers, businesses and educational institutions. We can be contacted at (888) 748-2583 or by visiting our website.
Your own personal cloud...
So just how are you using the cloud and what does your personal cloud contain? Music, photos, video, what else? If you give it some thought you might be surprised at how much you use "the cloud".
Over the past few years we've heard more and more about "the cloud". At first it seemed to be some sort of mythical, magical wonderland but the truth is that the cloud is just the internet. I say "just the internet" as if it means nothing but the internet is of course much bigger than that. Mbaonline recently posted an Infographic detailing a day in the life of the internet that demonstrates just how much we use the web! It's a pretty amazing graphic with some interesting statistics (daily iPhone sales outpace daily birth rates!).
Looking at the article got me thinking about the internet, the cloud and about how we access our personal data. Whether we realize it or not, many of us are developing our own personal cloud. Each day the use of web connected smart phones and tablet devices is growing as people are recognizing the value in staying connected. Companies like Evernote have developed great applications that let us share notes between devices and access them anywhere we like. Apple and Google both give users the ability to store music on the web instead of their home computer and access it from anywhere we like.
For our company, we use an application to provide a cloud based backup of our critical files and data (if you aren't backing your info up to the cloud you really should consider it). This particular product also gives us the ability to provide our staff and customers with a "Cloud Drive" on their computers. The Cloud Drive acts like any storage device (hard drive, USB flash drive, etc...) and lets you drag and drop files to it for storage. No matter where you are, as long as you have an internet connection you can access the files from any device including smart phones, tablets and traditional computers. I often use it for storing information I may need for a meeting. That way, I have it available to me at any time! One of our customers uses it to allow their marketing team to save information to it so that the sales team can access the information anytime, anywhere on their tablets.
So just how are you using the cloud and what does your personal cloud contain? Music, photos, video, what else? If you give it some thought you might be surprised at how much you use "the cloud".
Gone Phishin'
Sadly, that's not a "typo" in the title, but a reference to a nasty little practice that some folks have of trying to get you to visit a malicious site and give up your personal information. According to Wikipedia, "Phising is a way of attempting to acquire information such as usernames, passwords and credit card details by masquerading as a trustworthy entity in an electronic communication."
Most often, your e-mail is the primary target for phishing scams although various social networking sites are sometimes utilized by scammers to make posts with links to the offending site. You can't really blame your e-mail client, ISP or favorite social networking site, these messages arrive with professional-looking logos and legitimate looking documentation that’s extremely convincing. All that's required to spring the trap is for you to follow the link they provide!
Clicking the link may take you to a very legitimate looking site that asks you to confirm your login information, social security numbers, passwords, etc... In fact, some phishing attempts have become so sophisticated that they can send you to a legitimate site (a bank for example) and then generate a pop-up window that asks you to confirm your information. In this case, the main page underneath the pop-up is a legitimate site, the pop-up is the actual scam!
So how can you avoid phishing scams?
If you receive an e-mail asking you to visit a Web site, you can find out who’s behind the message by checking the sender’s e-mail through WHOIS, before you click anything! Here’s how to do it:
- DO NOT CLICK THAT LINK!
- Hover your mouse over the link and copy the domain for the address that your e-mail client (Outlook for example) displays. If you can't click inside the address box and highlight it, copy it down on a piece of paper. The domain is the component that is in front of dot com. For instance, the domain for http://bluelinenetworksolutions.com/ is bluelinenetworksolutions .
- Point your Web browser to http://www.whois.net.
- Enter the domain from the e-mail’s link in the WHOIS Lookup control and click Go.
- WHOIS will display details about the site, including the company or person who registered it.
If your e-mail’s supposedly from a bank or legitimate institution but is registered to some company you never heard of, or even an individual out of the country, chances are this is a phishing attempt! Do yourself a favor and don't take the bait!
It's possible that the info you receive from WHOIS still doesn't provide you with the answer that you need. In that case, try to track down the phone number or actual website address for the company and see if things are legitimate. I remember a recent e-mail I received where all of the information was credible except for a phone number that was provided in the e-mail. When I tracked the legitimate company down I found out that they were aware of the scam being perpetrated in their name and an investigation was underway!
A few tips for avoiding phishing scams are:
- If you receive an e-mail asking you to confirm information for your bank, credit card company, etc.. and it contains a link, don't follow the link. Close the e-mail and visit your bank's site the way you normally would.
- Always make sure you are entering private information in on a secure website. These sites start with "https://" and a small "lock" icon will appear to confirm that the site is secure. If you click the lock icon the site's security information will come up and you can see who it is registered to.
- Keep a close watch on the actual url of the site that you are at. For example, the text may say one thing but the link may lead you someplace else. In otherwords, if the link is supposed to go to "www.myfavoritebank.com" but the address in the toolbar says "www.yougotphished.com" then you need to get out fast!
If you'd like more information on how you can avoid phishing attacks, the FTC has published an article that can be found HERE. If you'd like more information on Blueline Network Solutions please feel free to visit our website at http://bluelinenetworksolutions.com or check us out on Facebook at https://www.facebook.com/Shopblueline.
How to Setup a Simple Multi-Account Avaya Meet-Me Conference
The free and built-in 6-party Avaya Meet-Me Conference feature is often missed or not setup. To get you started, we’ve put together a quick and simple five step administration guide for you.
1201 = “The number you have entered is invalid. Please enter the number again.”
1202 = “The number entered is invalid. Please contact the conference call coordinator to make sure you have the correct information. Goodbye.”
1203 = “Your conference call is already in progress.”
1204 = “You are the first party to join the call.”
1205 = “This meet-me conference is filled to capacity. Please contact the conference call coordinator for assistance. Goodbye.”
1206 = “If you have a security code, please enter it now or simply press the pound sign to continue.”
STEP 5: SETUP THE MEET-ME INDIVIDUAL ACCOUNT VDN’S 14XX: [add vdn 1401]
In this example you can setup up to 100 individual Meet-Me accounts (14XX) pointed to the same vector 251, however the limit really depends on your server type and needed PSTN trunking for external callers.
In this example, the following ranges were used:
- Extensions 1200 through 1206 = Meet-Me Announcements (should be non-DID)
- Extension 4000 = Main Meet-Me Access (should be a DID and optionally associated with a toll-free number)
- Extensions 1401 through 1499 = Individual Meet-Me Accounts (only 1401 setup in our example however additional accounts can be configured for people, groups or even conference rooms)
STEP 1: SETUP THE MEET-ME ANNOUNCEMENTS 1200-1206: [add announcement 1200]
Record the following announcements:
1200 = “Welcome to the XYZ Company Conference Center. Please enter your bridge number.”1201 = “The number you have entered is invalid. Please enter the number again.”
1202 = “The number entered is invalid. Please contact the conference call coordinator to make sure you have the correct information. Goodbye.”
1203 = “Your conference call is already in progress.”
1204 = “You are the first party to join the call.”
1205 = “This meet-me conference is filled to capacity. Please contact the conference call coordinator for assistance. Goodbye.”
1206 = “If you have a security code, please enter it now or simply press the pound sign to continue.”
STEP 2: SETUP THE MEET-ME MAIN ACCESS VECTOR 250: [change vector 250]
STEP 3: SETUP THE MEET-ME MAIN ACCESS VDN 4000: [add vdn 4000]
STEP 4: SETUP THE MEET-ME ACCOUNT VECTOR 251: [change vector 251]
STEP 5: SETUP THE MEET-ME INDIVIDUAL ACCOUNT VDN’S 14XX: [add vdn 1401]
In this example you can setup up to 100 individual Meet-Me accounts (14XX) pointed to the same vector 251, however the limit really depends on your server type and needed PSTN trunking for external callers.
To use the 6-party Meet-Me Conferencing in this configuration, the account holder of x1401 would send out an invite for the following ad-hoc meeting: (XXX) XXX-4000 x1401 (internal users only have to dial x1401)
Notes: Meet-Me Conference is available with R11 or higher (CMx) software. Meet-Me passwords were not setup in this example however can be added.Enjoy!
Why Should You Consider a Managed Anti-Virus Solution.
Technorati Blog Claim: WVZ37KR2VK6G
Every minute counts in today’s business. Stop wasting your valuable and scarce IT resource time and energy on the selection, testing, planning, deployment, updating and reporting of your Anti-virus software. Managed Anti Virus service provides the skilled IT resources, domain expertise, centralized monitoring and management facilities and proactive approach to ensuring the protection of your desktops and laptops against the ever present threat of viruses, spam and malware attacks.
Every minute counts in today’s business. Stop wasting your valuable and scarce IT resource time and energy on the selection, testing, planning, deployment, updating and reporting of your Anti-virus software. Managed Anti Virus service provides the skilled IT resources, domain expertise, centralized monitoring and management facilities and proactive approach to ensuring the protection of your desktops and laptops against the ever present threat of viruses, spam and malware attacks.
A managed Anti-virus solution can provide you with the peace of mind of knowing that your system is up to date, that scans are being run when they are supposed to be, and that a trained IT expert is looking out for your security. You no longer have to worry that someone may have disabled their Anti-virus software because it was "scanning while they were working" or wonder if they latest security updates have been downloaded and properly installed.
Advantages of a Managed Anti-Virus
• Provides proactive & comprehensive security, monitoring and management
• Centralizes the deployment and updating of software to ensure coverage and consistency
• Automates management processes to avoid errors and reduce costs
• Leverages expert IT skills
The truth is that having a better anti-virus solution is really just the tip of the iceberg in terms of the benefits that you receive. A fully managed anti-virus solution also delivers advanced business solutions such as:
- Enterprise Class Solution - Encompassing more than just anti-virus, this solution supports full endpoint security, providing you with an enterprise class method to combat viruses, malware, trojans and other malicious software.
- Comprehensive Reporting - A wide range of detailed reports are provided to ensure you have visibility into what is happening and assurance that you are protected.
- Fully Monitored System - We monitor the software to ensure it is working, has the latest virus definitions and we'll act immediately if there is an issue, potentially saving you from an attack.
- Network Health Monitoring Included - We monitor the health of your network, servers and workstations with daily maintenance checks including memory, processor and drive usage to proactively discover issues before they impact your business.
- Centralized management - Each machine is kept up to date directly from a centralized server. You no longer have to rely on end -users to manage their anti-virus.
While the list of features and benefits that a managed Anti-virus solution provide to your business is huge, the price is generally not much more than you are probably paying for your current Anti-virus solution. Here at Blueline Network Solutions we provide a managed Anti-virus solution not only to our business customers, but to our residential ones as well. Viruses are getting smarter and smarter everyday, isn't it about time your Anti-virus solution got smarter too?
If you'd like more information on how a managed Anti-virus solution can benefit your home or business, feel free to visit our website or give us a call at (888) 748-BLUE.
Google Web Fonts is integrated into Network Solutions’ Website Builder Tool
The Google Web Fonts team is proud to announce that Network Solutions have integrated our service with their Website Builder Tool.
Network Solutions is one of the largest domain registrars. When you register a domain with them, you can quickly and easily create a website using the Website Builder Tool. In the Page Editor, you can simply select a font from a drop down list in the typography palette for any text area:
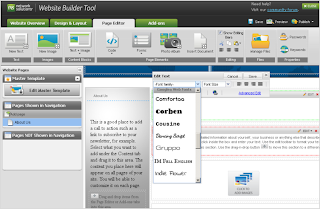
Get a domain from Network Solutions, create your site and you’re good to go with web typography!
Read more at the Network Solutions blog.
Are you a web developer, looking to present our growing collection to your users? If so, you should definitely check out the Google Web Fonts Developer API, which allows convenient programmatic access to a list of all fonts in the directory.
Posted by Dave Crossland, Font Consultant, Google Web Fonts
Network Solutions is one of the largest domain registrars. When you register a domain with them, you can quickly and easily create a website using the Website Builder Tool. In the Page Editor, you can simply select a font from a drop down list in the typography palette for any text area:
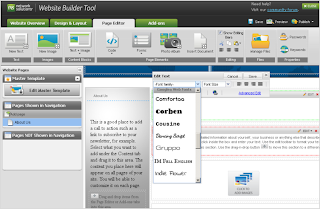
Get a domain from Network Solutions, create your site and you’re good to go with web typography!
Read more at the Network Solutions blog.
Are you a web developer, looking to present our growing collection to your users? If so, you should definitely check out the Google Web Fonts Developer API, which allows convenient programmatic access to a list of all fonts in the directory.
Posted by Dave Crossland, Font Consultant, Google Web Fonts
Web Fonts, now more compressed
One of Google’s core principles is that "fast is better than slow", and the Web Fonts team takes that to heart. We’re always looking for ways to make web fonts load faster, and that’s doubtless a key factor in our rapid user adoption. Today, we are announcing a new way to make web fonts smaller and faster, in collaboration with the Monotype Imaging Fonts.com Web Fonts team. Google Web Fonts now implements Monotype Imaging’s MicroType Express compression format, which yields an approximate 15% savings in file size over using gzip alone. This change will automatically speed up Google Web Fonts for Internet Explorer browsers (version 6 and up). We’re also actively working to offer improved compression with other modern browsers, including Google Chrome.
We’ve kept the interface simple, so designers don’t need to update their integrations in any way — we’ll automatically upgrade the CSS snippet and font files so that site designers and visitors get their fonts faster. We’ve done this for previous speed optimizations as well, such as automatically stripping the hints (metadata used for improving rendering quality on Windows) when serving fonts to Mac, iOS, and Android clients. We expect that most future optimizations will also be automatic and transparent.
Monotype Imaging has agreed to make MicroType Express available to the public at no cost; the license can be found at monotypeimaging.com/aboutus/mtx-license. We believe it’s friendly to both open source and proprietary implementations.
Today, we are also releasing an implementation of MicroType Express compression as part of the Embedded OpenType converter in the open-source sfntly library, adding to the existing WOFF compression. The sfntly library, developed by the Google Internationalization Engineering team, serves as the core conversion engine in Google Web Fonts for subsetting, hint stripping, and related functions of our dynamic serving path. We hope that all web font services, as well as people hosting their own web fonts, will use sfntly to optimize font serving across the web.
We are proud to be working with Monotype Imaging, and we look forward to learning more from designers, users, sites and other partners to advance the state of web fonts together!
Posted by Raph Levien, Engineer, Google Web Fonts
We’ve kept the interface simple, so designers don’t need to update their integrations in any way — we’ll automatically upgrade the CSS snippet and font files so that site designers and visitors get their fonts faster. We’ve done this for previous speed optimizations as well, such as automatically stripping the hints (metadata used for improving rendering quality on Windows) when serving fonts to Mac, iOS, and Android clients. We expect that most future optimizations will also be automatic and transparent.
Monotype Imaging has agreed to make MicroType Express available to the public at no cost; the license can be found at monotypeimaging.com/aboutus/mtx-license. We believe it’s friendly to both open source and proprietary implementations.
Today, we are also releasing an implementation of MicroType Express compression as part of the Embedded OpenType converter in the open-source sfntly library, adding to the existing WOFF compression. The sfntly library, developed by the Google Internationalization Engineering team, serves as the core conversion engine in Google Web Fonts for subsetting, hint stripping, and related functions of our dynamic serving path. We hope that all web font services, as well as people hosting their own web fonts, will use sfntly to optimize font serving across the web.
We are proud to be working with Monotype Imaging, and we look forward to learning more from designers, users, sites and other partners to advance the state of web fonts together!
Posted by Raph Levien, Engineer, Google Web Fonts
Subscribe to:
Posts (Atom)























